In the realm of cybersecurity, staying ahead of potential threats is paramount. One method employed...


Experience security from within. Our Authenticated Penetration Testing mirrors a privileged user, revealing internal soft spots. Strengthen your internal defenses to significantly enhance your resilience against external threats.

See yourself as attackers do. Our Unauthenticated Penetration Testing assesses your defenses from an outsider's perspective, fortifying your barriers where they're most susceptible.

Enhance your defenses with precision. Our Automated Penetration Testing provides a thorough security sweep, utilizing advanced technology to identify and address vulnerabilities rapidly.

Experience security from within. Our Authenticated Penetration Testing mirrors a privileged user, revealing internal soft spots. Strengthen your internal defenses to significantly enhance your resilience against external threats.

See yourself as attackers do. Our Unauthenticated Penetration Testing assesses your defenses from an outsider's perspective, fortifying your barriers where they're most susceptible.

Enhance your defenses with precision. Our Automated Penetration Testing provides a thorough security sweep, utilizing advanced technology to identify and address vulnerabilities rapidly.

Navigate the maze of regulations with confidence. From SOC 2 to ISO, we're your compass, ensuring you're compliant and ahead of the curve.

Simplifying the Complex Landscape of Compliance
Navigate the maze of regulations with confidence. From SOC 2 to ISO, we're your compass, ensuring you're compliant and ahead of the curve.
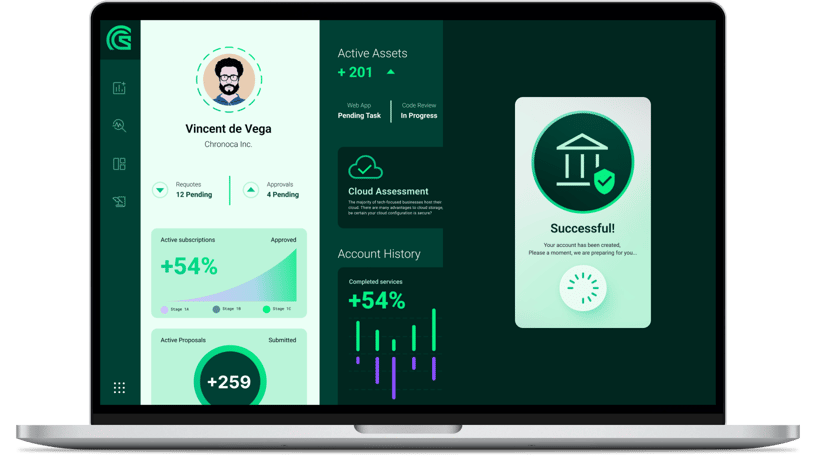
Empower your defense with Cacilian's specialized Pen Testing platform. Enhance your cybersecurity posture, shaped around your unique challenges, backed by our unmatched expertise and adaptability. Together, we’ll chart a secure digital journey.
Empower your defense with Cacilian's specialized Pen Testing portal. Enhance your cybersecurity posture, shaped around your unique challenges, backed by our unmatched expertise and adaptability. Together, we’ll chart a secure digital journey.
Traditional penetration testing offers security snapshots at intervals, but threats don't operate on a schedule. Cacilian’s Penetration Testing platform, through its simplified and frictionless approach, provides adaptive assessments utilizing advanced monitoring tools to evaluate defenses against evolving threats. This strategy ensures resilience against both current and emerging cyber risks, offering an efficient solution for your penetration testing needs.


Cybersecurity can be intricate, but interacting with it shouldn’t be. Our platform integrates user-focused design principles, immediately showcasing security posture, test status, and readiness metrics. No need to juggle interfaces—here, you can swiftly analyze vulnerabilities, collaborate with experts, and schedule tests.

Traditional penetration testing offers security snapshots at intervals, but threats don't operate on a schedule. Cacilian’s Penetration Testing portal, through its simplified and frictionless approach, provides adaptive assessments utilizing advanced monitoring tools to evaluate defenses against evolving threats. This strategy ensures resilience against both current and emerging cyber risks, offering an efficient solution for your penetration testing needs.

Cybersecurity can be intricate, but interacting with it shouldn’t be. Our platform integrates user-focused design principles, immediately showcasing security posture, test status, and readiness metrics. No need to juggle interfaces—here, you can swiftly analyze vulnerabilities, collaborate with experts, and schedule tests.

Real-time monitoring and addressing of threats.

A platform that transforms complexity into actionable insights.

An integrative approach for a streamlined experience and better ROI.

Real-time monitoring and addressing of threats.

A platform that transforms complexity into actionable insights.

An integrative approach for a streamlined experience and better ROI.
With our impenetrable data defenses, businesses can prioritize growth and innovation, confident in the security of their assets. Such assurance fosters a climate of operational efficiency and unbridled progress.
With our impenetrable data defenses, businesses can prioritize growth and innovation, confident in the security of their assets. Such assurance fosters a climate of operational efficiency and unbridled progress.
We make the unforeseen seen, ensuring surprises are
reserved for birthday parties, not board meetings.

Confront security threats head-on with in-depth unauthenticated and authenticated penetration tests.
Don't let vulnerabilities surprise you.

Our intuitive platform gets straight to the point, streamlining your security processes and providing a transparent overview of the dashboard within our penetration testing platform.
.png)
Eliminate the struggle of switching between systems. Our integration partner role enables seamless connections with Vanta.
We make the unforeseen seen, ensuring surprises are
reserved for birthday parties, not board meetings.

Confront security threats head-on with in-depth unauthenticated and authenticated penetration tests.
Don't let vulnerabilities surprise you.

Our intuitive platform gets straight to the point, streamlining your security processes and providing a transparent overview of the dashboard within our penetration testing portal.
.png)
Eliminate the struggle of switching between systems. Our integration partner role enables seamless connections with major GRC platforms such as Vanta and Secureframe, along with a variety of others.
Dive into our curated collection of articles, updates, and expert takes. In our blog, we shed light on the ever-evolving world of cybersecurity, share valuable tips, and offer perspectives that matter. Stay informed, stay secure.
Dive into our curated collection of articles, updates, and expert takes. In our blog, we shed light on the ever-evolving world of cybersecurity, share valuable tips, and offer perspectives that matter. Stay informed, stay secure.
Elevate your security with Cacilian's cutting-edge features and robust protocols.
Elevate your security with Cacilian's cutting-edge features and robust protocols.